Have you ever just finished building a load of PCs, to have someone come up and ask for some dodgy piece of hardware to be installed on all PCs, and the drivers required are unsigned, and aren't pre-packaged in an easily deployable silent package or MSI. Or you've been given some dodgy new hardware (you know the companies I'm talking of), to install.
Well its easier than you think to deploy drivers as either a script or as part of an MSI package. I am assuming that you, the reader, are capable of writing a script and/or creating a suitable MSI, so I will not insult your intelligence by giving you a completed script/msi. If you're anything like me (God help you if you are!) you'll learn better by doing, rather than seeing.
Anyway, by using a small executable provide by Microsoft, DPInst.exe, available as part of the Windows Driver Kit (WDK), Download available here, we can indeed make drivers available on any windows OS system, to be installed as and when needed.
Well its easier than you think to deploy drivers as either a script or as part of an MSI package. I am assuming that you, the reader, are capable of writing a script and/or creating a suitable MSI, so I will not insult your intelligence by giving you a completed script/msi. If you're anything like me (God help you if you are!) you'll learn better by doing, rather than seeing.
Anyway, by using a small executable provide by Microsoft, DPInst.exe, available as part of the Windows Driver Kit (WDK), Download available here, we can indeed make drivers available on any windows OS system, to be installed as and when needed.
Once you have download and installed the WDK (btw you only need to install the tools part), you can find different architectural/language versions of the DPInst.exe in C:\WinDDK\7600.16385.1\redist\DIFx\dpinst (assuming you install to the default location, and the version number hasn’t changed since writing).
Place the correct version of DPInst.exe in with your driver .inf files. If you were to run the dpinst.exe now, you would be presented with a wizard for installing the drivers onto the system. If you were to step through the wizard, it will complete, but it will only be successfully if the drivers are signed.
Place the correct version of DPInst.exe in with your driver .inf files. If you were to run the dpinst.exe now, you would be presented with a wizard for installing the drivers onto the system. If you were to step through the wizard, it will complete, but it will only be successfully if the drivers are signed.
However, that’s not what we really want, we need no user interaction at all, and we need to be able to install unsigned driver*. To install any drivers without the end user noticing, call the DPInst.exe with the following commands:
/Q - This is for quiet install with no user interaction,
/LM – This is for unsigned drivers.
/LM – This is for unsigned drivers.
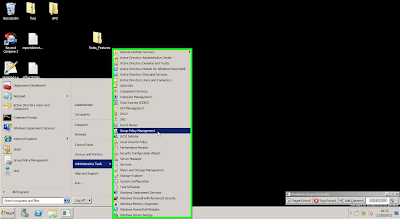
Now the drivers are installed, or technically they are made available to be installed when the hardware is connected. Now if your drivers are signed that is the end of the story, however, if like me, you have been given a host of cheap hardware made in china, with unsigned drivers, you will need to adjust the following 2 Group Policies*:
Policy: “Load and unload device drivers”
Setting: DomainName\Domain Users
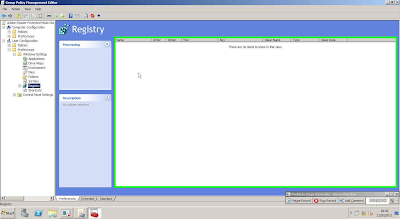
User Configuration>Admin Templates>System>Driver Installation:
Policy: “Code signing for device drivers”
Setting: Enabled – ignore
* Please note that installing unsigned drivers and/or modifying Group Policy is done at the readers own risk, and the writers of “Thoughts of a Primary School Tech” are in no way responsible/liable for any loss/damage caused to any system(s) by following the instructions provided here. Whilst every effort has been made to ensure this works correctly on any windows system, your milage may vary.